We assist the victims anywhere in Australia of business email compromise scams (BEC Scams) to recover lost monies by quickly and expertly identifying the likely source of the fraud or scam. These scams are also known as email scam or invoice fraud. Contact us on 08 8278 1779 or email reception@kruselegal.com.au
We are one of very few IT literate lawyers who do know how to :
- gather and interpret the forensic detail hidden in email headers and log files required to prove the email fraud
- provide a preliminary opinion based upon the email headers.
- negotiate with likely source of the scam, which is usually a solicitor, a real estate agent, a conveyancer or some other business that has requsted payment into their Trust Account – only for the victim to find out that the scammer has control of their email account (the “compromise”) and the victim has just sent money to the wrong trust account.
- advise what legal remedies are available to pursue the business or their insurer in the courts if co-operation isn’t given
- intiate proceedings in a Federal Court, (thereby bypassing any inter-state jurisdictional problems) to extract co-operation if it hasn’t been given using the court’s discovery processes and it’s power to compel disclosure
- engage a internationally recognised forensic IT expert to give an expert opinion (if required).
The good news is that most businesses that operate a trust account have insurance. We expect swift co-operation from the business or their insurer.
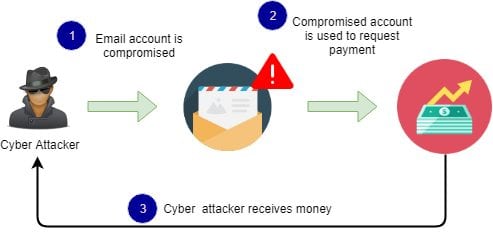
The Australian Cyber Security Centre defines Business email compromise (BEC) as “an online scam where a cybercriminal impersonates a business representative to trick you, an employee, customer or vendor into transferring money or sensitive information to the scammer.”
Key advice
You need to move quickly (1) If you’ve sent money or personal banking details to a scammer contact your bank immediately.
You need to move quickly (2) because the evidence required to prove the source of the email scam can be lost as older log files get overwritten. To assist, initially we will only need a copy of the fraudulent email you relied upon and it’s headers. Usually it will be only slightly different to an earlier legitimate email.
Contact us on 08 8278 1779 or email reception@kruselegal.com.au
The police are usually not interested. They will take a statement, but because the bad guy is “somewhere in cyberspace”, they usually can’t take any action. The federal police are usually not much better.
You will be referred to ACORN. Doing this is basically a waste of your time as it only helps the Commonwealth Government to gather statistics. Your report just goes into “into a black hole”.
Check to see if your account has previously been compromised at haveibeenpwned.com , then change your email password anyway.
The business email compromise scam – explained
This section is taken from https://www.cyber.gov.au/threats/business-email-compromise
To begin, a cybercriminal impersonates a trusted person using an email address that appears to be legitimate (this is known as “masquerading”). To do this, they may use a username that is almost identical to the trusted person’s name, or a domain that is almost identical to the name of the trusted person’s company. Alternatively, they could replace the “from” or “reply-to” text with the trusted person’s exact email address (this is called email “spoofing”), or they could even gain remote access to the trusted person’s actual email account.
The cybercriminal then sends a legitimate-looking message to the target requesting money or sensitive information.
BEC usually takes one of four basic forms:
- Executive fraud: The cybercriminal successfully masquerades an executive’s email address and then sends a message to staff in your business directing them to transfer funds to the scammer’s account.
- Legal impersonation: The cybercriminal masquerades as a lawyer or legal firm representative requesting payment for an urgent and sensitive matter.
- Invoice fraud: The cybercriminal masquerades as a trusted supplier and sends a fake invoice to your business. In these scams, the cybercriminal often has control of the supplier’s email account and can access legitimate invoices. The cybercriminal changes these invoices to include new bank account details and then sends the invoices to customers from the supplier’s email account.
- Data theft: Instead of requesting funds, a cybercriminal may masquerade as a trusted person to request sensitive information. This information can then also be used as part of a larger and more damaging scam.
Because these scams don’t use malicious links or attachments, they can get past anti-virus programs and spam filters.